Data Sovereignty: Mastering Envelope Encryption with AWS KMS and EBS
Encryption is only as secure as its key management. Explore the architectural mechanics of AWS KMS and EBS volume encryption unraveling the lifecycle of Data Keys (DEKs), hypervisor orchestration, and the critical security paradigm of Envelope Encryption.
In the modern cloud, data is the most valuable and vulnerable asset. Safeguarding this data at rest is not just a best practice; it is a foundational requirement for compliance and sovereignty. AWS Key Management Service (KMS) serves as the high-security backbone of this layer, orchestrating the encryption of Amazon EBS volumes through a sophisticated process known as Envelope Encryption.
In this deep dive, we break down the lifecycle of an encryption key and how the AWS hypervisor manages data integrity across EC2 lifecycles.
The Paradigm of Envelope Encryption
AWS KMS does not encrypt your large data volumes directly with a master key. Instead, it uses a tiered approach:
- KMS Key (formerly CMK): Stays within the FIPS 140-2 Level 3 security boundary of KMS. It never leaves the service.
- Data Key (DEK): A unique key generated for each individual volume, used for the actual high-speed encryption/decryption of data.
The Lifecycle of an Encrypted EBS Volume
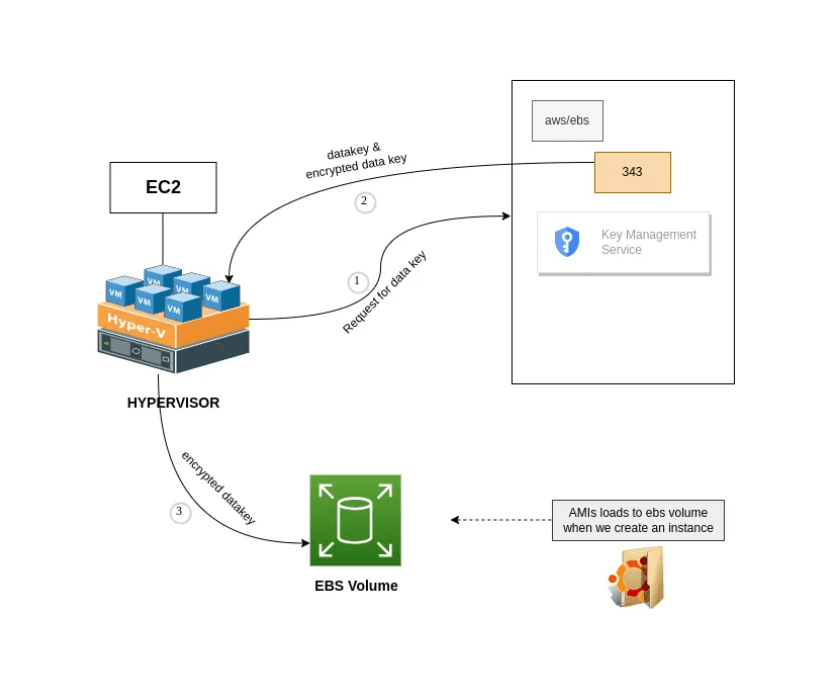
When you enable encryption on an EBS volume, a multi-stage cryptographic handshake occurs between the AWS hypervisor and the KMS service.
1. Data Key Generation
The hypervisor requests a data key from KMS. KMS generates a unique, random data key (e.g., a 256-bit AES string). However, KMS does not send this key in the clear. Instead, it designates the key for that specific volume and encrypts it using the AWS/EBS Master Key.
2. Metadata Integration
KMS provides the hypervisor with two versions of the key: the Plaintext Data Key and the Encrypted Data Key. While the hypervisor uses the plaintext key for active operations, it stores the Encrypted version as persistent metadata within the EBS volume itself. This ensures the key is always attached to the data it protects.
3. Transparent Encryption at Rest
Once the handshake is complete, all I/O operations are handled by the hypervisor. As data is written to the EBS volume, the hypervisor encrypts it on-the-fly using the plaintext data key. This process is transparent to your application, ensuring zero-latency performance impact.
Persistence vs. Volatility: The Stop/Start Lifecycle
To understand the security of this architecture, we must look at how keys behave during system state changes.
- Instance Active: The hypervisor retains the plaintext data key in its volatile memory to perform fast I/O operations.
- Instance Stopped: For security, when an EC2 instance is stopped, the hypervisor wipes the plaintext data key from its memory. At this stage, the data on the EBS volume is purely "at rest" and undecipherable.
- Instance Restart: Upon restart, the hypervisor retrieves the encrypted data key from the EBS metadata and sends it back to KMS. If the IAM permissions allow, KMS decrypts the key and returns the plaintext version to the hypervisor, allowing the instance to boot and access its data.
This ensures that if a physical drive were ever removed from an AWS data center, the data would remain an unintelligible blob because the decryption key is only available through a verified KMS handshake.
Governance: Key Policies and Service Integration
The true power of AWS KMS lies in its granular governance.
Key Policies
You can define exactly who or what can use your master keys. For example, you can grant an EC2 instance the right to use a key for decryption but deny it the right to manage or delete that key. This follows the Principle of Least Privilege.
Unified Integration
KMS is a global service. The same architectural patterns used for EBS can be applied to Amazon S3, RDS, and Lambda, allowing you to protect data across your entire stack without managing diverse, complex cryptographic libraries.
Conclusion
Envelope Encryption through AWS KMS turns key management from a bottleneck into a scalable security asset. By offloading the complexities of cryptography to AWS, engineers can focus on building resilient applications while maintaining total sovereignty over their data.
Understanding these fundamentals is the first step in building a truly secure cloud-native infrastructure.
Happy Securing! 🛡️🛰️
Fuel the Architecture
If this deep dive helped you build something better, consider fueling my next late-night coding session.
Newsletter Updates
Join 1,000+ engineers receiving weekly insights into AI, cloud architecture, and technical guides.