Orchestration Internals: Understanding the Ansible Execution Engine
Behind every high level Ansible command lies a sophisticated execution engine. We unravel the backend process from YAML parsing to ephemeral Python script injection that makes agentless automation possible.
In the world of configuration management, Ansible is often described as "magic" due to its agentless nature and human-readable syntax. However, beneath the YAML surface lies a meticulously engineered execution engine.
To master automation, one must understand the lifecycle of an Ansible command—the journey from a local terminal to a remote server state.
1. The Logic Transformation: YAML to Python
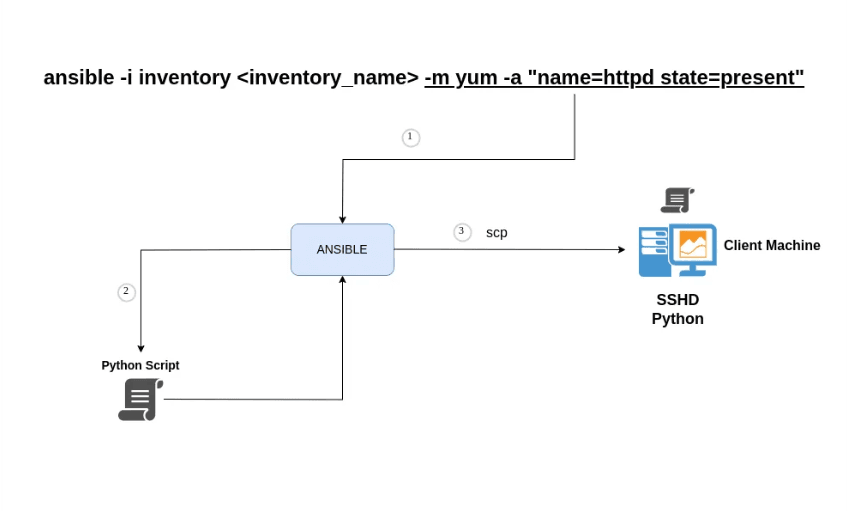
When you execute an Ansible playbook or an ad-hoc command, the engine doesn't simply "send" the YAML. Instead, it performs a Code Generation phase.
Ansible parses your instructions and transforms them into an ephemeral, self-contained Python script. This script includes the module logic (e.g., apt, yum, or copy) and the specific arguments you provided. This transformation is why Ansible can remain agentless; it doesn't need a dedicated client on the target—it just needs an interpreter that understands the script it generates.
2. The Secure Transport Layer (SSH & SCP)
Once the Python script is generated, it must be delivered to the target node. Ansible utilizes the Secure Shell (SSH) protocol as its primary transport mechanism.
The generated script is transferred to a temporary directory on the remote server using SCP (Secure Copy Protocol) or SFTP. This is why the remote server must have SSHD (Secure Shell Daemon) active and accessible. This "push" model eliminates the need for managing persistent daemon connections on every server in your fleet.
3. Remote Runtime Execution
After the script lands safely on the remote node, the final phase of the orchestration begins:
- Execution: Ansible executes the injected Python script using the remote system's Python interpreter.
- Telemetry Collection: The script performs its task (e.g., ensuring a service is running) and collects the result.
- Result Reporting: The script outputs a JSON-formatted response, which is captured by Ansible and sent back to your local machine.
- Self-Deletion: For security and cleanliness, Ansible automatically removes the temporary Python script from the remote server once execution is complete.
Critical Requirements for the Remote Node
For this "magic" to function, your target nodes must meet two foundational requirements:
- SSHD Active: To allow the transport of scripts.
- Python Interpreter: To execute the injected logic.
Why It Matters: The Power of Agentless Design
By unraveling these backend processes, we see the true genius of Ansible's architecture. It shifts the burden of complexity from the Target Node to the Control Node.
This allows you to manage thousands of diverse servers from cloud instances to networking hardware without ever having to install or upgrade specialized agent software on the targets themselves. It is automation reduced to its purest form: secure, ephemeral, and incredibly powerful.
For a visual breakdown of this process, check out the Engineering Internals video on our YT node.
Happy Orchestrating! 🤖🛰️
Fuel the Architecture
If this deep dive helped you build something better, consider fueling my next late-night coding session.
Newsletter Updates
Join 1,000+ engineers receiving weekly insights into AI, cloud architecture, and technical guides.